Today I will be walking you through how to tunnel snmp-check and other UDP traffic over SSH.
In this example we are tunnelling UDP over SSH to circumvent firewall rules on the outside. Our firewall rules are only allowing access into the other side of the firewall to TCP port 22 on a Ubuntu server. We don’t have access to any other TCP or UDP ports. The only method of communication into the environment is via SSH to our Ubuntu server. We will use this server as jump/pivot point for other traffic. Imagine we have earlier identified through cdpsnarf using SSH dynamic port forwarding and proxychains another router, we want to enumerate this further. Our next goal in this case is to try and enumerate SNMP UDP port 161 on target router with a public community string. This example could also be applied to all sorts of UDP traffic such as DNS for example were we want to tunnel our local DNS requests to a server behind a firewall. Zone transfer maybe?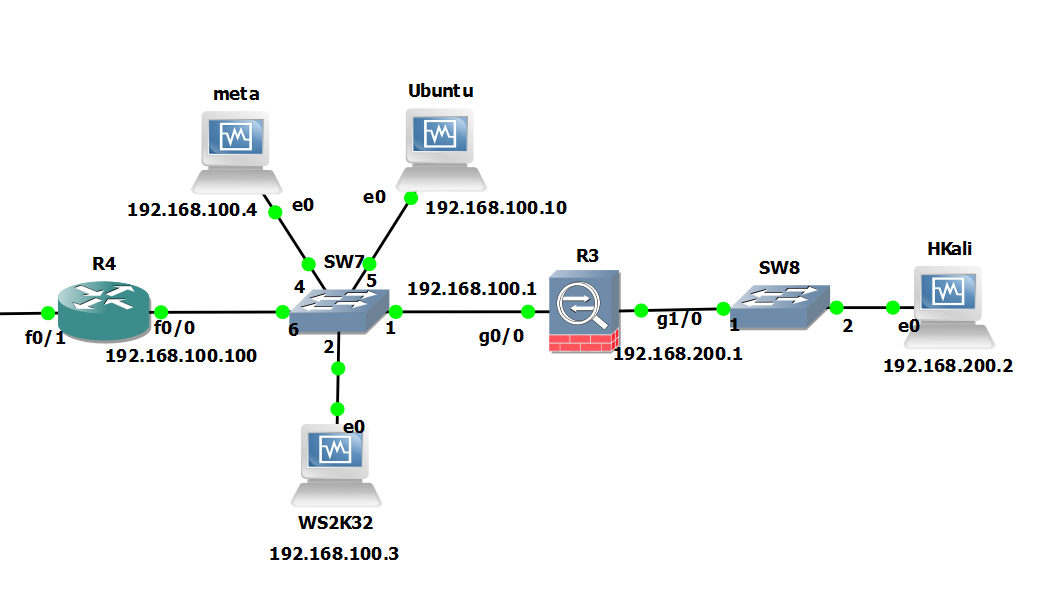
Attack machine: Kali Linux 192.168.200.2
Pivot Server: Ubuntu 192.168.100.10
Target: GNS3 Cisco Router 192.168.100.100
We are going to do this by sending our local UDP traffic through netcat (handling UDP) into a fifo process back into netcat (handling TCP), through the ssh tunnel then in reverse the other end. Yes I know bit of a brain teaser! You can read more about fifo files here, they are similar to pipe in linux. In essence we are sort of writing the output to a file (without actually writing anything) then sending it on its merry way through netcat via TCP then down the tunnel. Its best we see this in the flesh with an example.
We begin on the Attack machine by running up the ssh connection, here we are forwarding TCP port 6666 on localhost to TCP 6666 on the remote pivot server:
root@kali:~# ssh -L 6666:localhost:6666 user@192.168.100.10
Then on the Pivot Server we create a fifo file for netcat to talk too:
root@ubuntu:/home/user# mkfifo /tmp/fifo root@ubuntu:/home/user# nc -l -p 6666 < /tmp/fifo | nc -u 192.168.100.100 161 > /tmp/fifo
On the Attack machine we do similar:
root@kali:~# mkfifo /tmp/fifo root@kali:~# nc -l -u -p 161 < /tmp/fifo | nc localhost 6666 > /tmp/fifo
In second terminal on the attack machine:
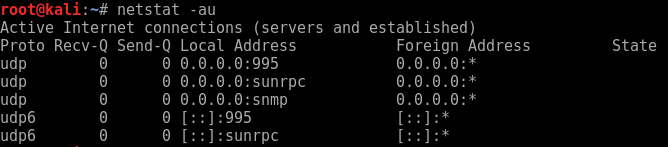
Run up ‘netstat -au’ to verify snmp is listening on the local machine.
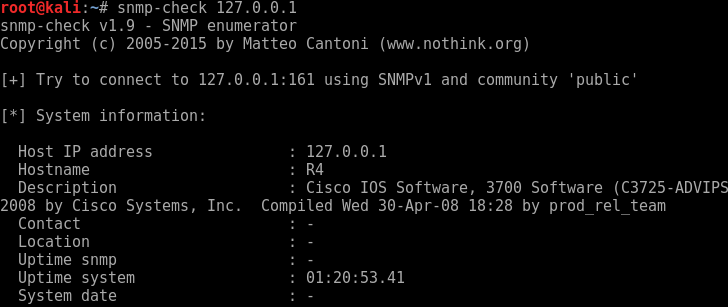
We can then simple run snmp-check to localhost.
snmp-check 127.0.0.1
Looking further down the information we discover the following:
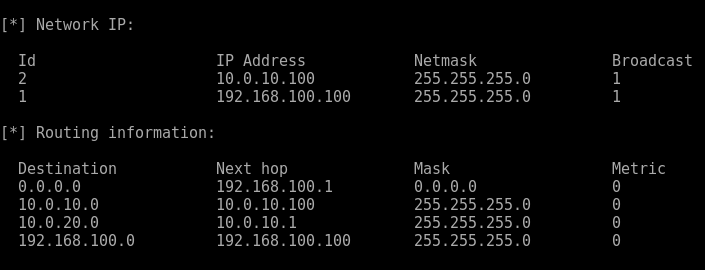
Another network interface, is this possibly the internal network and route to DA..? Maybe in the next post…
Bingo UDP and snmp-check over an SSH tunnel, awesome!
