Running MBSA on remote machine that is in a workgroup or different domain.
I thought I would share my findings on using MBSA (Microsoft Baseline Security Analyser) for targeting remote machines that are not part of the same domain or in a workgroup. This really is a great tool for enumerating OS patch levels.
We have two scenarios to run through; the first, running MBSA on remote machine that is in a different domain from the machine that it is installed on. The second, running MBSA on a machine that is in a workgroup. Ok no problem. Here is what we do.
First Scenario
In the first scenario our target machine is a Windows Server 2012 R2 machine that is in a different domain to our MBSA host (Windows 7 Pro 64bit). Fire up a cmd prompt with admin privileges from the machine that you are running MBSA from, and run the following syntax:
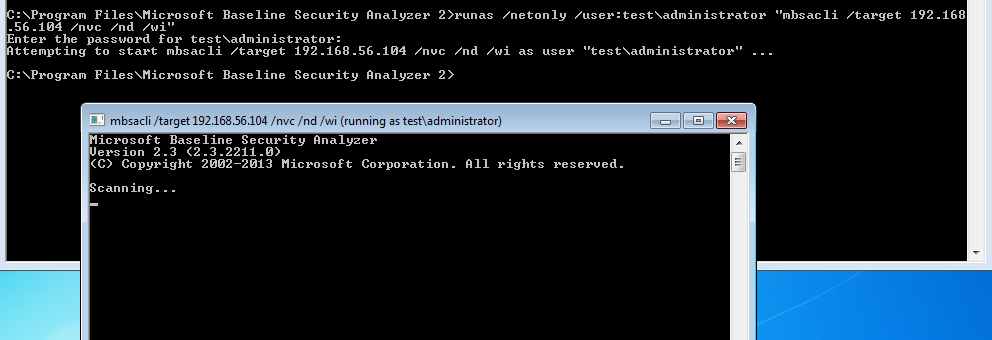
runas /netonly /user:test\administrator "mbsacli.exe /target 192.168.56.104 /nvc /nd /wi"
A second command prompt will pop up and run, running the syntax as above:
If you wait a short while the MBSA command prompt will disappear when finished, from here you can open up MBSA and view the report:
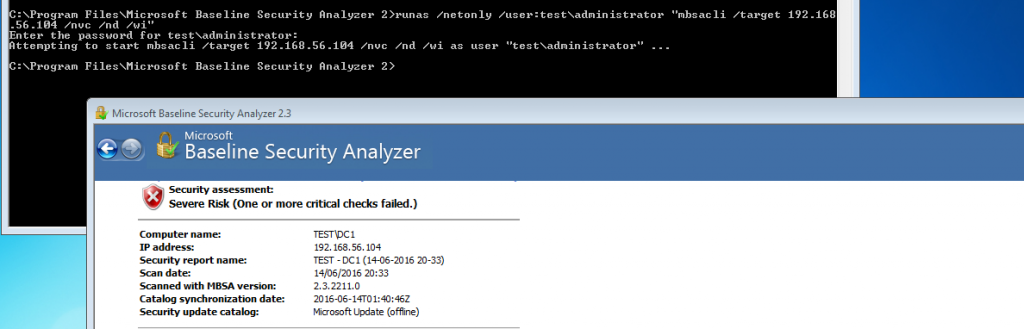
In this example the target machine was in my virtualbox lab, in a domain called ‘Test’. The machine I ran MBSA from was a Windows 7 Pro machine in a workgroup (no relationship) other than IP connectivity. The cli syntax I used here was used to speed up the check, clearly only use this if you have the latest scan catalogue:
/wi – Show all updates even if not approved by wsus.
/nvc – Do not check for a new version of MBSA.
/nd – Do not download any files from MS update site when scanning.
Additional options:
/target <Target-IP>
/listfile C:\tmp\targets.txt
/catalog C:\tmp\wsusscn2.cab
Add: ‘>C:\tmp\MBSADC1.txt’ to the end of the syntax for a handy output to a text file.
As an example you might use:
runas /netonly /user:test\administrator "mbsacli /catalog C:\tmp\wsusscn2.cab /target 192.168.56.104 /nvc /nd /wi"
The Second Scenario
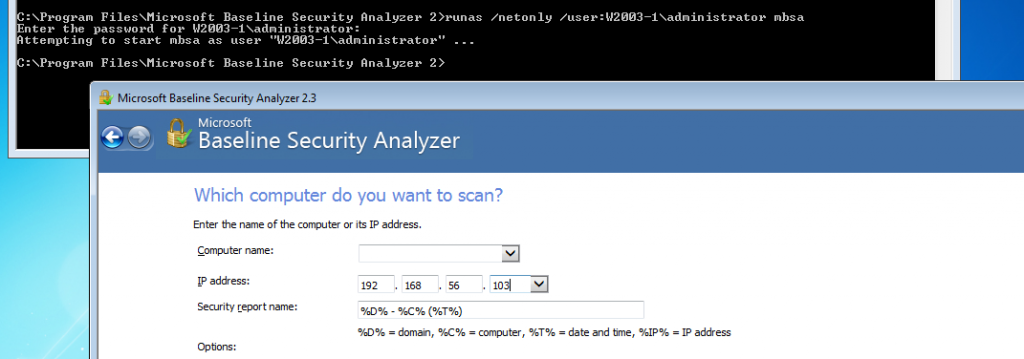
The second scenarios is a Windows Server 2003 machine that is in workgroup. The syntax is actually the same however your specifying the local machine name rather than the domain name. I have mixed this one up a little here by not using the cli, by just specifying MBSA the command simple fires up MBSA GUI as the account specified. The only thing to remember here is to add the IP address into the GUI.
runas /netonly /user:test\administrator mbsa
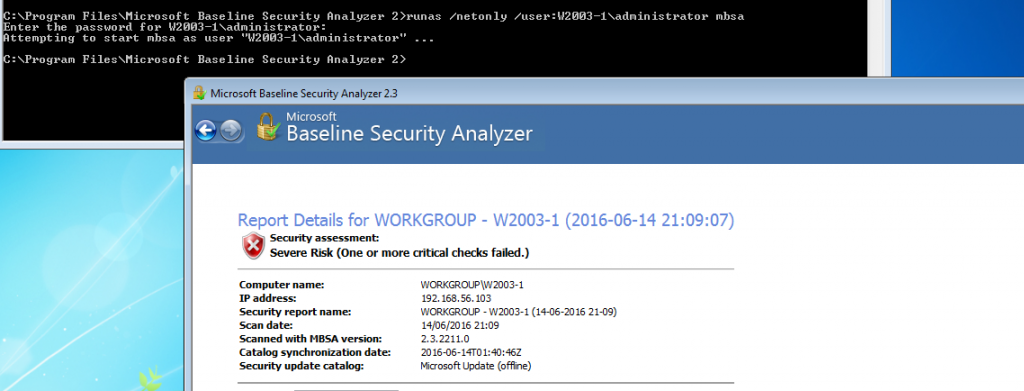
And again after the scan has finished the results can be view in the GUI.
I haven’t successfully managed to do this from a Windows 10 client yet, various forums would suggest it isn’t supposed to work with 10 however if you know please feel free to drop me an email or comment.
