The Exploit-db.com needs no introduction. Most penetration testers will be well versed in the use of Exploit-db and its uses. However for new-comers, this is an excellent and ‘the go to’ resource when looking for exploits and exploit code for use in test labs on vulnerable systems. It goes without saying though when looking through code that is published on the internet the following precautions should be taken;
- Review the code. Understand what the code is doing.
- Modify the code if needed to suit your situation, especially any shellcode snippets.
- Understand what lanuguage the code is written in.
- Don’t run code from the internet without knowing what the code is going to do. You don’t want to create a reverse shell back to a C&C server do you.
- Always test code in a lab, isolated from the internet and production systems.
- Understand that some code such as C++ and C for example will most likely need compiling and need dependancies.

Searching Exploit-db.com
There are several ways to search the Exploit-db such as:
- Via the exploit-db site: https://www.exploit-db.com/ however when searching for exploits you will have to use their captcher form in order to proceed with a search.
- Via Google search engine using the syntax: ‘SITE:Exploit-db.com Windows Privilege Escalation’
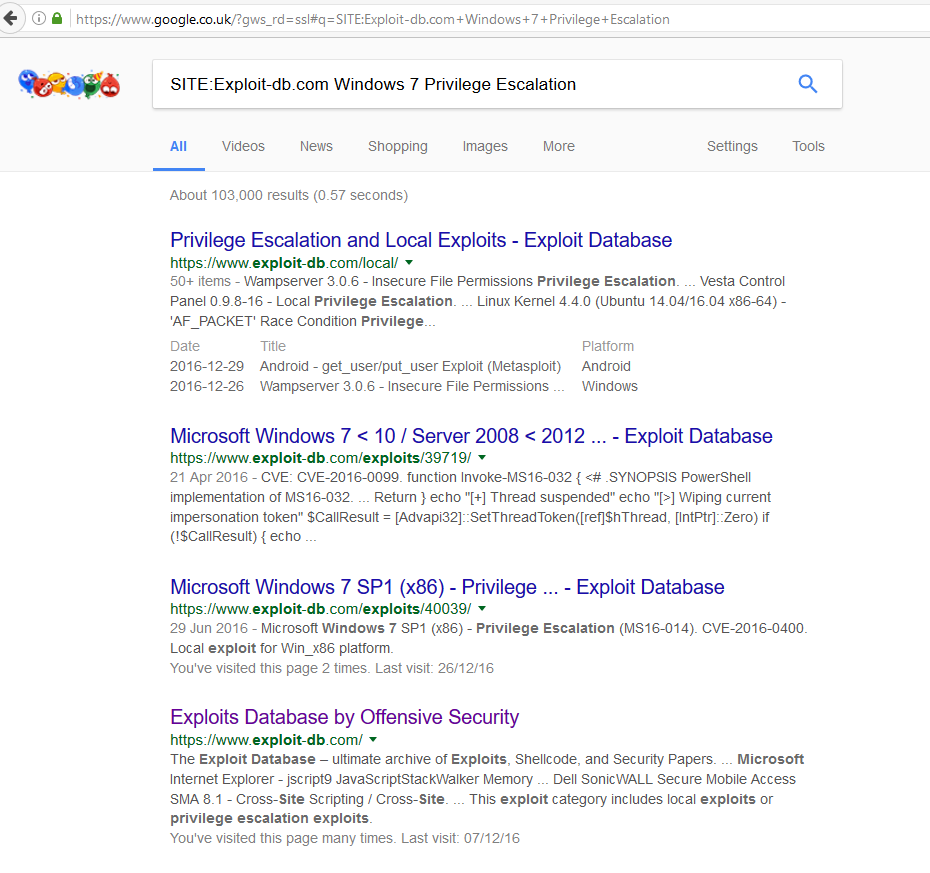
Google search of the Exploit-DB - Using searchsploit built into Kali Linux like below, this has the added benefit that the databse is offline:
root@kali:~# searchsploit windows 7 Privilege Escalation
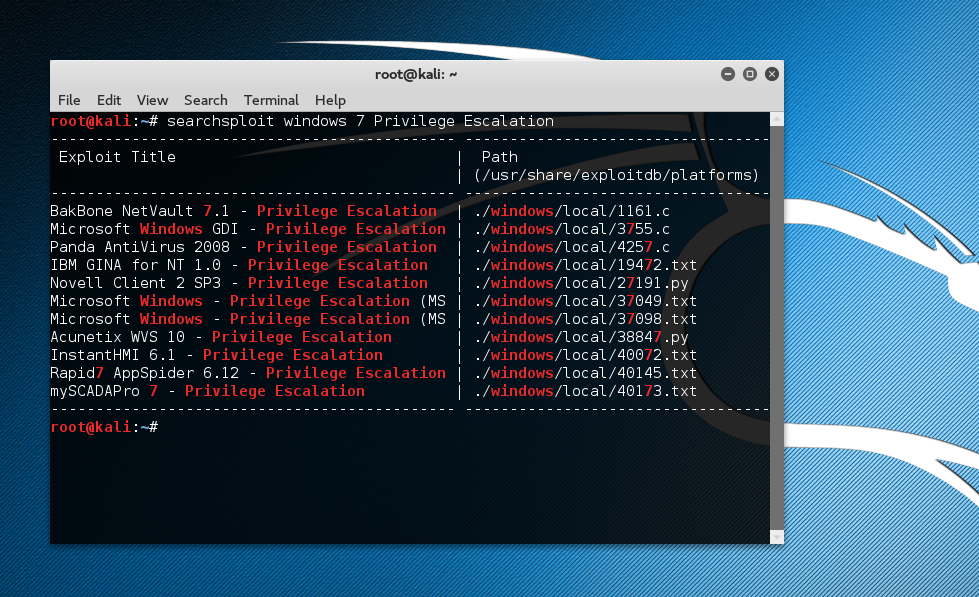
The offline copy can be updated with:
root@kali:~# searchsploit -u
Hope you find this useful.
